DORA Regulation: How it will affect third-party management?
The Digital Operational Resilience Act (DORA) introduces new measures for financial firms to address third-party risks. DORA emphasizes risk management procedures and due diligence on third-party providers. Firms must monitor their activities and conduct regular assessments of their own resilience.
The Digital Operational Resilience Act (DORA Regulation), formally established under Regulation (EU) 2022/2554, introduces a comprehensive, unified framework aimed explicitly at strengthening ICT risk management, regulating third-party ICT service provider risks, and establishing detailed incident reporting requirements across the entire EU financial sector. DORA replaces fragmented and sector-specific ICT requirements with standardized, enforceable regulations that provide clear directives on governance structures, internal control systems, comprehensive contractual management, rigorous resilience testing, and robust supervisory enforcement mechanisms.
This document delineates regulatory mandates into technical specifications, exhaustive procedural guidelines, and precise control measures designed to enable compliance officers, IT governance teams, and senior management to practically implement and operationalize the extensive requirements outlined in DORA, ensuring full regulatory compliance well before the stipulated enforcement deadline of January 17, 2025.
Introduction to the DORA Regulation
The Digital Operational Resilience Act (DORA Regulation) emerges as a crucial legislative response to an increasingly sophisticated cyber threat landscape and the growing reliance of financial services on digital infrastructures. Officially enacted by the European Parliament and the Council of the European Union in December 2022, DORA is encapsulated under Regulation (EU) 2022/2554, supplemented by specific Delegated Regulations, notably Regulation (EU) 2024/1772 addressing comprehensive incident reporting and Regulation (EU) 2024/1774 focusing on the oversight of critical ICT third-party providers.
DORA consolidates and supersedes existing ICT-related mandates drawn from prominent EU directives and regulations, including the Capital Requirements Directive IV (CRD IV), Payment Services Directive 2 (PSD2), Solvency II, European Market Infrastructure Regulation (EMIR), and Markets in Financial Instruments Directive II (MiFID II). By unifying previously disparate regulatory requirements, DORA significantly reduces compliance complexity and promotes supervisory coherence among the key European Supervisory Authorities—namely the European Banking Authority (EBA), the European Insurance and Occupational Pensions Authority (EIOPA), and the European Securities and Markets Authority (ESMA).
Central to DORA’s objectives is the continuous, secure, and resilient delivery of critical financial services. This is achieved by mandating a systematic, lifecycle-based approach to ICT risk management, explicitly embedding accountability at the highest management level, particularly within the boards of financial institutions. Furthermore, DORA mandates proactive and rigorous oversight of external ICT dependencies, emphasizing stringent due diligence, detailed contractual agreements, continuous performance monitoring, and extensive resilience testing to mitigate risks associated with third-party ICT service providers. This strategic emphasis ensures financial entities maintain optimal preparedness and resilience in the face of digital disruptions.
DORA Regulation: Scope, Applicability, and Exemptions
The Digital Operational Resilience Act (DORA) establishes a comprehensive regulatory framework that applies to every financial entity established within the European Union. Below is a detailed breakdown of DORA's scope, its applicability to various market participants, and the specific exemptions provided by the regulation.
Scope of DORA
Broad Applicability Across Financial Entities:
DORA is designed to cover a wide array of financial entities to ensure a harmonized approach towards ICT risk management and operational resilience across the EU. This includes, but is not limited to:
- Credit Institutions: Banks and other deposit-taking institutions.
- Investment Firms: Entities involved in asset management, brokerage, and other investment services.
- Insurance Companies: Both life and non-life insurers.
- Payment Institutions and Electronic Money Institutions: Providers of payment services and electronic money, ensuring secure payment processing.
- Crowdfunding Platforms: Online platforms facilitating capital raising from a broad investor base.
- Crypto‑Asset Service Providers: Entities offering services such as crypto trading, custody, and exchange of digital assets.
Each of these entities is required to comply with a unified set of rules and standards that promote robust ICT risk management practices, as explicitly stated in Article 2 of Regulation (EU) 2022/2554.
Inclusion of Non‑EU Firms with EU Operations:
DORA’s jurisdiction is not limited solely to EU‑headquartered firms. Non‑EU companies that operate branches or establish a business presence within the European Union are also subject to its provisions. This inclusion ensures that any financial services offered within the EU’s internal market, regardless of the firm’s country of origin, must meet the same high standards of ICT risk management and operational resilience.
Applicability Details
Comprehensive Regulatory Coverage:
The regulatory framework is applicable to all the financial entities mentioned above. This means that each entity must:
- Develop and maintain an ICT risk management framework aligned with DORA's requirements.
- Regularly update risk registers, implement continuous monitoring, and conduct periodic stress tests.
- Integrate ICT risk management into overall governance practices, including senior management oversight and board-level accountability.
Critical or Important Functions (CIFs):
Entities must identify and map out their Critical or Important Functions (CIFs) — these are operations or services whose disruption would result in significant financial, operational, or reputational damage. The classification of CIFs is essential as it drives the prioritization of ICT risk mitigation measures. This process involves:
- A detailed inventory of all ICT assets.
- Mapping interdependencies between ICT systems and business functions.
- Implementing risk controls proportionate to the criticality of these functions.
Exemptions Under DORA
Exemption for Microenterprises:
To prevent disproportionate regulatory burdens on smaller entities, DORA explicitly exempts microenterprises from the full spectrum of ICT risk management obligations. The regulatory text defines microenterprises as organizations with fewer than 10 employees and an annual turnover below €2 million (Art 2(4)). However, even though these entities are exempt from comprehensive ICT risk management requirements, they are still required to report major ICT incidents. This ensures that while the operational and compliance burden is reduced for smaller firms, systemic risks are not ignored.
Implications for Third‑Party Service Providers:
DORA also extends its regulatory framework to external ICT third‑party service providers (TPPs) that support Critical or Important Functions. When a TPP is designated as a Critical Third‑Party Provider (CTPP), it becomes directly subject to DORA’s requirements. This includes:
- Mandatory due diligence and contractual obligations.
- Compliance with specific risk management standards and oversight measures as mandated by the regulation.
- Regular assessments and reporting requirements to ensure that any service disruption does not compromise the operational resilience of the financial entities that rely on these services.
Digital Operational Resilience Act: Regulatory Terminology
A foundational step toward compliance with the DORA Regulation (Regulation (EU) 2022/2554) is a precise, operational understanding of its core terminology. Each defined term below carries distinct compliance obligations — from governance requirements to reporting protocols — and is referenced by specific Articles in DORA and its Delegated Regulations.
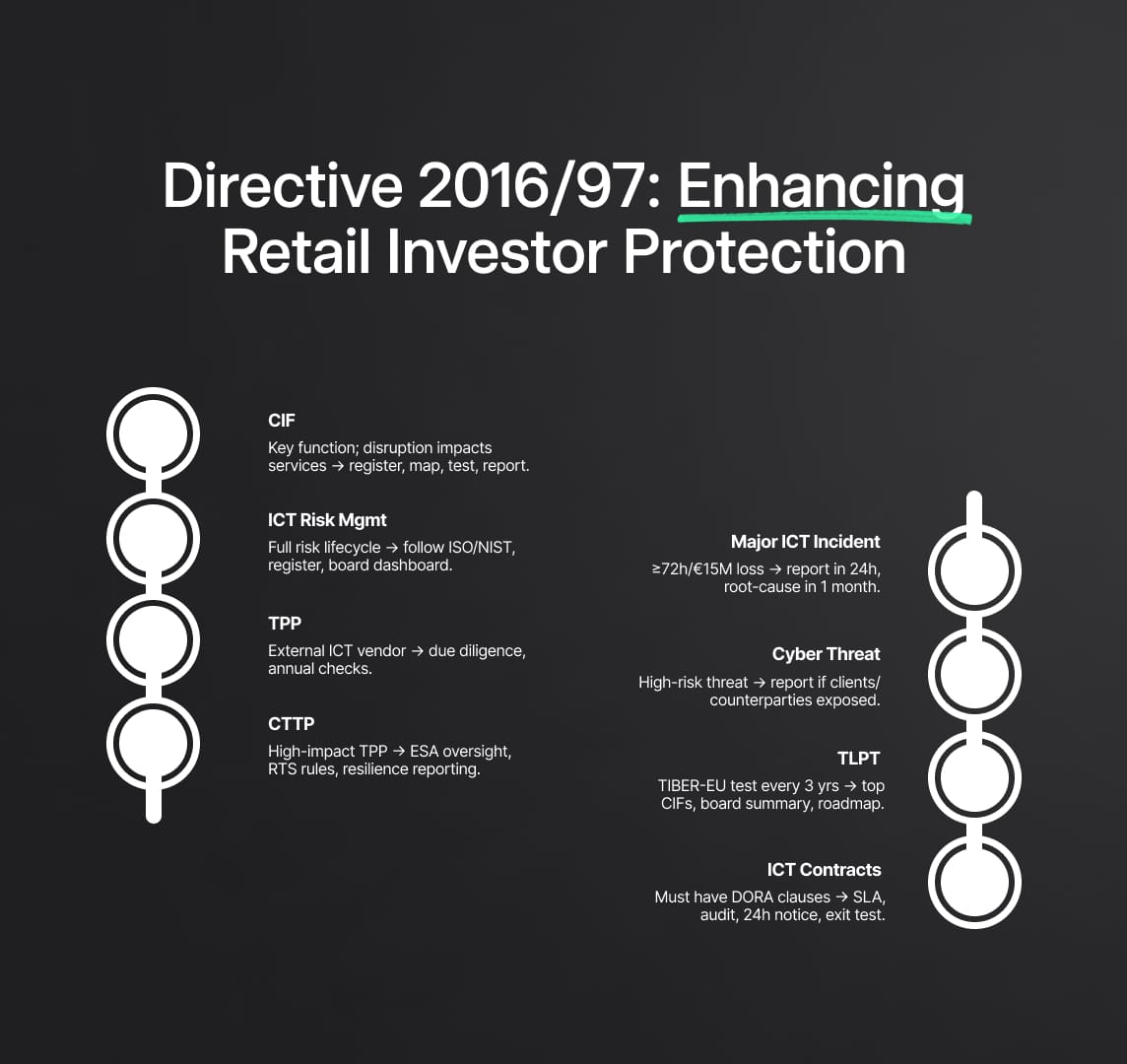
Critical or Important Function (CIF)
Definition: Under Article 3(13), a Critical or Important Function (CIF) is any business activity, process, or service whose disruption would materially impair the provision of financial services, leading to significant financial loss (>€10 million/day), customer impact (>50,000 customers), or systemic contagion risk.
Regulatory Implication: Entities must maintain a CIF register, updated quarterly, mapping each CIF to underlying ICT assets, third‑party dependencies, and recovery objectives (RTO ≤4 hours, RPO ≤2 hours). CIF classification drives proportional controls, resilience testing scope, and supervisory reporting obligations (Art 24, Art 25).
ICT Risk Management
Definition: Defined in Article 4, ICT Risk Management encompasses the end-to-end lifecycle of identifying, assessing, mitigating, monitoring, and reporting ICT-related risks.
Regulatory Implication: Requires adoption of recognized frameworks (ISO/IEC 27005, NIST SP 800‑30), formal risk registers, documented control frameworks, and quarterly board-approved risk dashboards (Art 26–27).
ICT Third‑Party Service Provider (TPP)
Definition: Article 3(17) defines a TPP as any external vendor providing hardware, software, infrastructure, or cloud services supporting CIFs.
Regulatory Implication: Entities must execute enhanced due diligence prior to onboarding, including financial health checks, cybersecurity certification verification (ISO 27001, SOC 2), and independent penetration test reports. Annual reviews and contractual renewal risk assessments are mandatory (Art 28).
Critical Third‑Party Provider (CTPP)
Definition: Article 28(6) and Delegated Regulation (EU) 2024/1774 designate a CTPP based on criteria such as EU market share (>5%), substitutability, and concentration risk.
Regulatory Implication: Once designated, CTPPs are subject to direct supervision by ESAs, annual resilience reporting, and binding Regulatory Technical Standards (RTS) compliance — including third‑party risk policies, audit rights, and exit strategies.
Major ICT Incident
Definition: Per Article 17, a Major ICT Incident is any event causing ≥72 hours of CIF disruption, financial losses ≥€15 million, or significant data integrity compromise.
Regulatory Implication: Triggers mandatory notification to the competent authority within 24 hours via the EU Incident Reporting Portal and submission of a root-cause analysis report within one month, formatted to STIX/TAXII threat intelligence standards (Art 18–20, Reg 2024/1772).
Significant Cyber Threat
Definition: A credible threat with high probability of causing a Major ICT Incident, identified through threat intelligence and vulnerability scanning.
Regulatory Implication: Voluntary reporting encouraged; mandatory client and counterparty notification if exposure risk is detected (Art 17).
Threat‑Led Penetration Testing (TLPT)
Definition: Article 25(4) mandates adversary-simulated penetration testing aligned with the ECB’s TIBER‑EU framework, conducted at least every three years for systemically important entities.
Regulatory Implication: TLPT scope must cover top three CIFs, produce detailed attack narratives, quantified impact scoring, prioritized remediation roadmaps, and board-level executive summaries.
4.8 ICT Third‑Party Contractual Arrangement
Definition: Formal written agreements governing the provision of ICT services by TPPs, specifying service descriptions, data protection measures, audit rights, and exit strategies.
Regulatory Implication: Must include mandatory DORA model clauses (Art 30), with stricter requirements for CIFAs: quantitative SLAs (≥99.9% uptime), 24-hour incident notification, unrestricted audit and inspection, and annual exit plan testing.
DORA: Governance and Accountability Requirements
The DORA Regulation embeds accountability for digital operational resilience at the management body level, mandating explicit governance structures, resource commitments, and documented oversight mechanisms.
Management Body Accountability (Art 21)
The board of directors or equivalent governing body holds “full and ultimate accountability” for:
- Approving the ICT Risk Appetite Statement with clear tolerances (RTO ≤4 hours; RPO ≤2 hours).
- Allocating at least 3% of annual IT expenditure to digital resilience investments (security controls, redundancy, third‑party oversight tools).
- Endorsing the ICT Governance Charter, defining decision-making hierarchies, roles, and escalation paths.
Senior Management and ICT Risk Committee
A formal ICT Risk Committee, chaired by the Chief Information Security Officer (CISO) or Chief Risk Officer (CRO), must convene quarterly to:
- Review the live ICT Risk Register, challenge residual risk ratings, and validate emerging threat intelligence.
- Approve remediation action plans with clear deadlines, resource assignments, and success metrics.
- Oversee third‑party risk assessments, contract renewals, and exit plan validations.
Organizational Roles and Segregation of Duties
Clear delineation of ICT risk functions is required to prevent conflicts of interest:
- Chief Information Security Officer (CISO): Strategic cybersecurity oversight and incident response leadership.
- Senior ICT Risk Officer: Third‑party risk governance, contract lifecycle management, ICT register maintenance.
- Internal Audit: Independent validation of ICT risk controls and governance effectiveness on an annual basis.
Governance Documentation and Review
Entities must maintain and review the following policies and plans at least annually:
- ICT Risk Management Policy: Scope, risk taxonomy, assessment methodologies, and escalation protocols.
- Third‑Party Risk Management Policy: Due diligence criteria, contractual frameworks, ongoing monitoring requirements.
- Incident Response Plan: Detection, classification, escalation, reporting, and post-incident review procedures.
- Business Continuity & Disaster Recovery Plans: CIF-specific recovery objectives, failover procedures, and periodic simulation exercises.
Reporting, Metrics, and Escalation Protocols
Quarterly board reports must include:
- Top five residual ICT risks with heatmap visualizations and trend analyses.
- Key Risk Indicators (KRIs): Mean Time to Detect (MTTD ≤15 minutes), Mean Time to Remediate (MTTR ≤24 hours), patch compliance (≥98% within 30 days).
- Third‑party performance dashboard: SLA adherence rates, audit findings, exit readiness scores.
Escalation triggers must be predefined, with immediate notification to the competent authority for any Major ICT Incident, material third‑party failure, or breach of risk appetite thresholds.

The ICT Risk Management Lifecycle Explained
The Digital Operational Resilience Act (DORA Regulation) mandates a holistic, continuous ICT risk management lifecycle comprising four interdependent phases: Risk Identification, Risk Assessment, Risk Mitigation, and Risk Monitoring (Art 24–27). Each phase is governed by specific regulatory requirements, performance metrics, and governance controls to ensure measurable digital resilience across all Critical or Important Functions (CIFs).
Risk Identification
Under Article 24, financial entities must develop and maintain a Dynamic Asset Inventory that catalogs every ICT asset, application, data repository, and interdependency supporting CIFs. Identification activities must include:
- Asset Mapping: Document system names, owners, data classification levels, and data flow diagrams.
- Dependency Analysis: Map upstream/downstream dependencies to third-party services, internal interfaces, and legacy systems.
- Criticality Classification: Assign quantitative scores (High/Medium/Low) using thresholds for financial impact (>€10M/day), customer impact (>50,000 users), and reputational risk indices. Entities must update the CIF register quarterly and upon any material change (e.g., new vendor onboarding).
Risk Assessment
Article 25 requires a hybrid risk scoring methodology combining technical vulnerability analysis with business impact assessments:
- Technical Scoring: Apply CVSSv4 to enumerate vulnerability severity, exploitability, and impact metrics for each ICT asset.
- Business Impact Assessment Score (BIAS): Rate business consequences using a 1–5 scale across financial, operational, legal, and reputational dimensions.
- Risk Matrix & Residual Risk Calculation: Calculate inherent risk (CVSSv4 × BIAS), apply control effectiveness factors, and record residual risk in a centralized Risk Register.
Entities must conduct formal risk assessments at least annually, and more frequently for high-criticality assets or following significant incidents or technology changes. All assessments require documented approval by senior management.
Risk Mitigation
Article 26 prescribes layered controls tailored to asset criticality and residual risk:
- Preventive Controls: Multi-factor authentication (MFA), AES‑256 encryption at rest and in transit, network microsegmentation, secure coding standards.
- Detective Controls: Security Information and Event Management (SIEM) with User and Entity Behavior Analytics (UEBA), automated log aggregation, anomaly detection algorithms (MTTD ≤15 minutes).
- Corrective Controls: Automated patch management workflows, incident playbooks with predefined decision trees, rollback procedures, and root-cause remediation timelines (MTTR ≤24 hours).
Entities must document control implementation evidence, conduct monthly vulnerability scans, and remediate high-severity findings within 30 days.
Risk Monitoring and Reporting
Article 27 mandates continuous monitoring supported by integrated telemetry, quarterly control effectiveness reviews, and real-time dashboards:
- Key Risk Indicators (KRIs): Patch compliance rate (≥98%), number of unresolved high-risk vulnerabilities, SLA breach incidents, third-party performance metrics.
- Board-Level Reporting: Quarterly ICT Risk Reports must include heatmap visualizations of top residual risks, trend analysis against risk appetite thresholds, and exception reports for SLA breaches.
- Independent Validation: Internal Audit or an external third party must annually assess the maturity of the ICT Risk Management framework against ENISA and NIST Cybersecurity Framework standards.
Governance Integration
Governance oversight integrates lifecycle activities into enterprise risk management through defined escalation paths, documented in the ICT Governance Charter. The management body must review and approve risk appetite statements annually, ensuring alignment with strategic objectives and regulatory expectations (Art 21)
Detailed Incident Reporting Framework
DORA harmonizes incident reporting obligations by establishing precise classification criteria, reporting timelines, and content requirements for Major ICT Incidents and Significant Cyber Threats (Art 17–20). This section provides step-by-step guidance to ensure regulatory compliance, transparency, and effective stakeholder communication.
DORA: Incident Classification and Severity Levels
- Major ICT Incident: An event causing ≥72 hours of disruption to a CIF, financial losses ≥€15 million, significant data integrity compromise, or systemic contagion risk.
- Significant Cyber Threat: A credible threat with high likelihood of materializing into a Major ICT Incident, identified through threat intelligence feeds or vulnerability exploits.
Reporting Obligations for Major ICT Incidents
Under Article 17, entities must:
- Initial Notification: Submit a preliminary incident report to the competent authority within 24 hours of detection via the EU Incident Reporting Portal.
- Root-Cause Analysis Report: Deliver a comprehensive report within one month, detailing incident timeline (UTC timestamps), technical and business impact metrics, root cause, threat actor indicators (formatted in STIX/TAXII), remediation actions, and lessons learned.
Reporting Obligations for Significant Cyber Threats
Article 18 encourages voluntary reporting of high-risk threats. However, if client or counterparty exposure is detected, entities must issue a Mandatory Notification to affected stakeholders within 48 hours, providing actionable mitigation guidance.
Incident Report Content Requirements
All reports must adhere to Delegated Regulation (EU) 2024/1772 taxonomy and include:
- Incident classification and severity score
- Detailed description of affected CIFs and ICT assets
- Quantified impact assessment (financial, operational, reputational)
- Root-cause analysis with technical evidence and IOC indicators
- Mitigation measures taken and planned corrective actions
- Estimated recovery timelines and contingency measures
Incident Response and Escalation Process
Implement a documented Incident Response Playbook integrating Security Orchestration, Automation, and Response (SOAR) workflows:
- Automated detection and classification via SIEM/UEBA
- Immediate convening of Incident Response Team (IRT) within 1 hour
- Tiered escalation matrix defining roles, decision authority, and communication channels
- Regulatory notification triggers at predefined severity thresholds
- Post-incident review meeting within 10 business days to update controls and processes
Regulatory Templates and Submission
Use the EU Incident Reporting Portal’s standardized electronic forms for both initial and final reports. Ensure threat intelligence indicators are submitted in STIX/TAXII format to support cross-entity threat correlation.
Continuous Improvement and Documentation
Post-incident, conduct a Lessons Learned Workshop involving cross-functional stakeholders. Update the Incident Response Plan, revise risk assessments for affected assets, and document enhancements in the ICT Risk Register to prevent recurrence.

In‑Depth Digital Operational Resilience Testing Requirements
DORA (Regulation (EU) 2022/2554 Art 25) mandates a tiered resilience testing regime designed to validate the effectiveness of ICT controls, identify latent vulnerabilities, and ensure continuous improvement of digital operational resilience. This section details the regulatory requirements, methodologies, deliverables, and governance controls for both annual security testing and advanced Threat‑Led Penetration Testing (TLPT).
Annual Security and Resilience Testing (Art 25(1)–(3))
Scope & Frequency: All in‑scope financial entities (excluding microenterprises) must conduct annual security assessments on all ICT systems and applications supporting Critical or Important Functions (CIFs). Required activities include:
- Vulnerability Assessments: Automated scans aligned with CIS Benchmarks and OWASP Top 10, covering network, application, and container environments.
- Static and Dynamic Code Analysis: Integrate SAST/DAST tools into CI/CD pipelines to identify code-level vulnerabilities before production deployment.
- Configuration Reviews: Evaluate compliance against CIS Controls and NIST SP 800‑53 baselines for system hardening and secure configurations.
- Business Continuity & Disaster Recovery Drills: Annual tabletop exercises simulating CIF outage scenarios, validating RTO and RPO metrics.
Performance Metrics:
- Vulnerability remediation rate ≥95% for critical findings within 30 days.
- Configuration drift <2% across production systems.
- Successful recovery of CIF services within RTO and RPO thresholds.
Threat‑Led Penetration Testing (TLPT) (Art 25(4))
Regulatory Mandate: Systemically important entities must perform TLPT at least every three years, targeting their top three CIFs, following the ECB’s TIBER‑EU framework.【Reg (EU) 2024/1772】
TLPT Methodology & Deliverables:
| Deliverable | Description |
|---|---|
| Attack Narrative | Step‑by‑step description of adversary tactics, techniques, and procedures (TTPs) used during the test. |
| Impact Scoring Matrix | Quantitative assessment of confidentiality, integrity, availability impacts using CVSSv4 and BIAS methodology. |
| Remediation Roadmap | Prioritized action plan with estimated resource requirements, timelines, and control maturity targets. |
| Executive Summary | High‑level report for senior management and board, highlighting key risks, strategic recommendations, and residual risk ratings. |
Submission Requirements: Final TLPT reports and remediation status updates must be submitted to the competent authority via the EU Incident Reporting Portal within 30 days of test completion.
Independent Assurance & Audit
Entities must engage independent third‑party auditors annually to validate the effectiveness of resilience testing programs, review remediation evidence, and verify compliance with DORA technical standards (Art 25(5)).
Comprehensive Third‑Party ICT Risk Management Guidance
Articles 28–32 of DORA establish a rigorous framework for third‑party risk governance, requiring end‑to‑end due diligence, contract lifecycle management, continuous monitoring, and exit planning.
Pre-Contract Due Diligence (Art 28(2))
Entities must perform structured assessments of prospective ICT service providers, evaluating:
- Financial stability (minimum three years of audited financial statements).
- Cybersecurity posture (ISO 27001 certification, recent penetration test reports).
- Business continuity and disaster recovery plans.
- Subcontractor management policies and data sovereignty compliance.
Mandatory Contractual Requirements (Art 30)
Contracts must differentiate between CIF‑affecting (CIFA) and non‑CIFA arrangements, incorporating mandatory clauses for:
- Service Level Agreements: Uptime ≥99.9%, defined recovery objectives, and penalties for SLA breaches.
- Data Security: AES‑256 encryption at rest/in transit, data segregation controls.
- Audit & Inspection Rights: Unrestricted onsite inspections, remote audit access, and subcontractor transparency.
- Incident Notification: Notification within 24 hours for CIFA; within 48 hours for non‑CIFA.
- Exit & Transition Planning: Detailed playbooks with data retrieval formats, transfer protocols, and annual exit readiness tests.
Ongoing Monitoring & Third-Party Register (Art 28(3–5))
Maintain a centralized, searchable register of all ICT contracts, updated in real time to include:
- Provider risk rating (High/Medium/Low).
- CIF relevance and contract expiry dates.
- Subcontractor hierarchies and material change flags.
Annual submission to competent authority by March 31 must include new agreements, status changes, and exit plan readiness.
Exit & Termination Protocols
Define clear exit triggers (material breach, insolvency, non-compliance), data repatriation methods, escrow arrangements, and transition service agreements (TSAs).
Critical Third‑Party Provider (CTPP) Oversight Mechanisms
Delegated Regulation (EU) 2024/1774 establishes a rigorous oversight regime for Critical Third‑Party Providers (CTPPs), ensuring that the most systemically important ICT vendors adhere to the highest standards of digital operational resilience under the DORA Regulation.
Designation Criteria and Process (Reg 2024/1774 Art 4–6)
ESAs designate CTPPs based on quantitative thresholds for systemic importance, including:
- Market Share: Providers servicing >5% of EU financial sector revenue for a specific ICT service.
- Lack of Substitutability: High barriers to entry, proprietary technology dependencies, and absence of viable alternative suppliers.
- Concentration Risk: Top three providers controlling >60% of the market for a given ICT function.
The designation process involves data collection via the ESAs’ annual market survey, risk scoring against a standardized framework, and formal notification to both the provider and affected financial entities.
10.2 CTPP Obligations & Reporting Requirements
Designated CTPPs must comply with binding Regulatory Technical Standards (RTS) on ICT third‑party policies, and submit detailed annual reports to ESAs by March 31 each year. Reports must include:
- Governance Structure: Organizational chart, senior management accountability, and risk committees.
- Operational Resilience Metrics: SLA performance (availability ≥99.99%), Mean Time to Recover (MTTR ≤4 hours), incident frequency and severity.
- Security Testing Results: TLPT outcomes, vulnerability remediation statistics, and penetration test executive summaries.
- Business Continuity & Disaster Recovery Plans: Recovery time and recovery point objectives (RTO/RPO) for each critical service.
- Subcontractor Hierarchies: Detailed mapping of sub‑vendor relationships, risk assessments, and contractual safeguards.
10.3 Supervisory Powers and Enforcement
Under Art 28(8), ESAs hold direct supervisory authority to:
- Conduct Onsite Inspections: Including unannounced visits and deep-dive audits of operational processes and security controls.
- Issue Binding Instructions: Mandating corrective action plans with explicit deadlines (typically ≤90 days for high-risk findings).
- Impose Financial Sanctions: Fines up to 1% of annual global turnover for non-compliance with RTS or failure to remediate identified deficiencies.
- Suspend or Restrict Services: Temporarily prohibit the provision of critical ICT services until compliance gaps are addressed.
10.4 Remediation & Escalation Protocols
CTPPs must submit remediation progress reports every 30 days following an ESA directive. Failure to comply escalates to the European Commission for potential cross-border enforcement measures, including reputational sanctions and mandatory service termination.
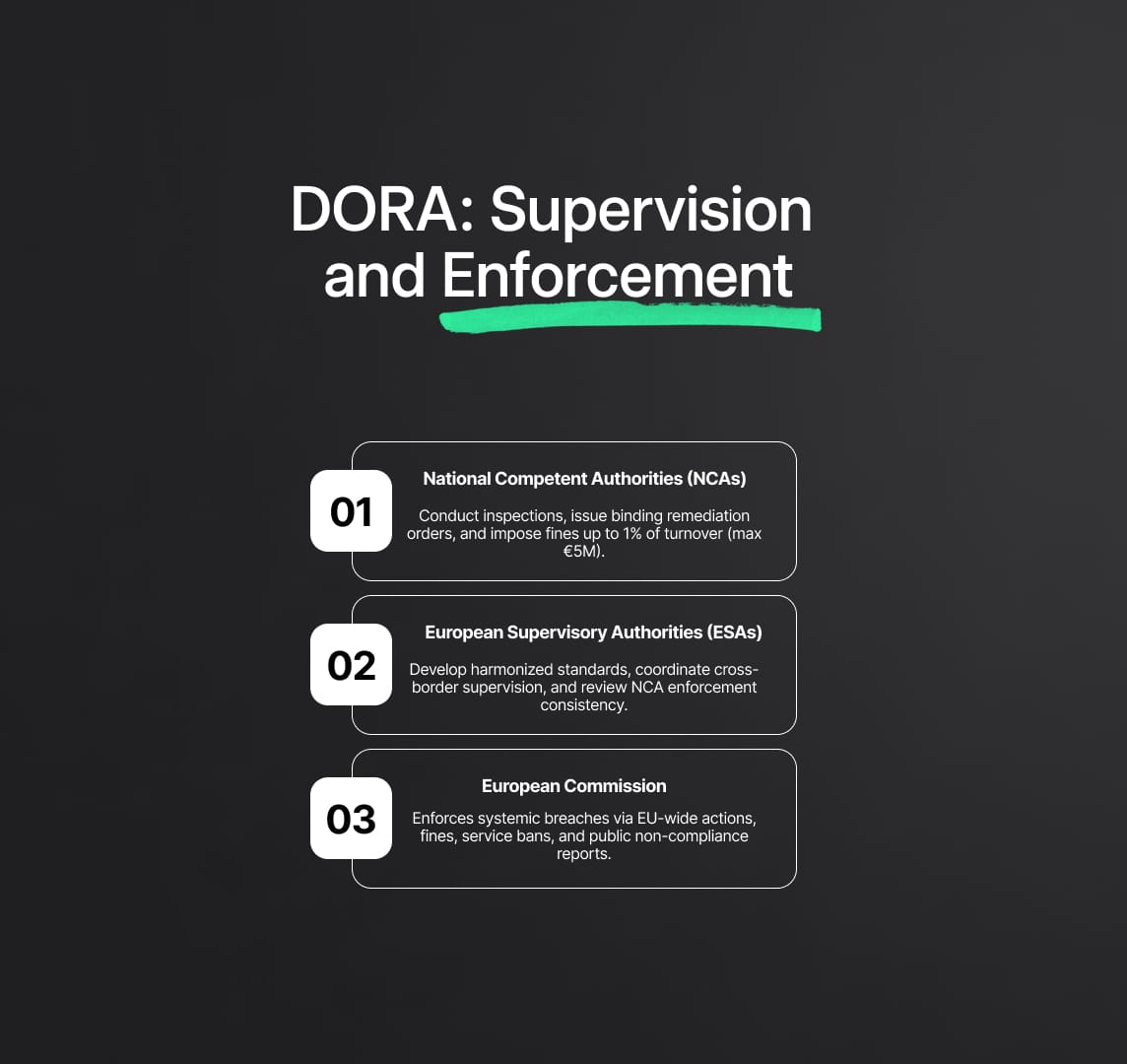
Supervisory Architecture and Enforcement Provisions The DORA Regulation
establishes a multi-layered supervisory framework that integrates national competent authorities (NCAs), the European Supervisory Authorities (ESAs), and the European Commission to ensure consistent enforcement across the EU financial sector.
Role of National Competent Authorities (Articles 63–66)
NCAs are the primary enforcers of DORA for financial entities within their jurisdiction. Their powers include:
- Onsite Inspections & Thematic Reviews: Conduct risk-based and scheduled examinations of ICT risk management frameworks, third‑party registers, and incident reporting processes.
- Binding Instructions & Corrective Action Plans: Issue formal orders requiring remediation within specified timelines (≤60 days for material weaknesses; ≤30 days for urgent issues).
- Administrative Sanctions: Impose fines up to 1% of annual turnover (capped at €5 million) for breaches of DORA requirements, with aggravated penalties for repeat violations or intentional non-compliance.
Role of European Supervisory Authorities
The EBA, EIOPA, and ESMA coordinate supervision through the ESAs’ Joint Committee, providing:
- Harmonized Guidelines & RTS: Develop binding standards to ensure consistency in risk assessment methodologies, third‑party oversight, and incident classification.
- Cross-Border Coordination: Facilitate information sharing and joint investigations for entities operating in multiple Member States.
- Peer Reviews: Assess NCA enforcement practices to identify supervisory divergences and recommend best practices.
European Commission Enforcement Mechanisms
For systemic or cross-border breaches, NCAs refer cases to the European Commission, which may:
- Issue EU-wide enforcement decisions mandating corrective actions across multiple jurisdictions.
- Levy cross-border fines or impose service suspensions at the EU level.
- Publish non-compliance reports, triggering reputational consequences and market scrutiny.
Step‑By‑Step DORA Implementation Roadmap
| Phase | Deadline | Key Deliverables | Actions |
|---|---|---|---|
| Governance & Inventory | Jan 17, 2025 | Approved ICT Governance Charter, CIF register | Map assets, define roles, set RTO/RPO thresholds |
| Incident Reporting | Jan 17, 2025 | Operational EU reporting portal integration | Configure SOAR, train IRT, test report templates |
| Third‑Party Compliance | Jul 17, 2025 | DORA‑compliant contracts, Third‑Party Register | Conduct due diligence, update contracts, submit register |
| TLPT Execution | Jan 17, 2027 | Completed TLPT for top 3 CIFs | Select testing provider, scope validation, submit results |
| Continuous Improvement | Ongoing | Quarterly risk dashboards, maturity assessments | Review metrics, update controls, executive reporting |
13. Frequently Asked Questions (FAQ)
Q1: What constitutes a Major ICT Incident under DORA? An event causing ≥72 hours of CIF disruption or ≥€15 million in losses, triggering notification within 24 hours and root-cause reporting within one month (Art 17–18).
Q2: When must the ICT Third‑Party Register be submitted? Annually by March 31, detailing all ICT contracts, provider risk ratings, CIF designations, and exit plan statuses (Art 28(3–5)).
Q3: Who qualifies as a Critical Third‑Party Provider (CTPP)? A TPP designated by ESAs based on systemic importance — market share >5%, lack of substitutability, concentration risk (Reg 2024/1774 Art 4).
Q4: What are the minimum metrics for resilience testing? MTTD ≤15 minutes; MTTR ≤24 hours; patch compliance ≥98% within 30 days; SLA uptime ≥99.9%.
Q5: How often must systemically important entities perform TLPT? Every three years, covering the top three CIFs under the ECB’s TIBER‑EU framework (Art 25(4)).
15. References and Regulatory Citations
Regulation (EU) 2022/2554 (Digital Operational Resilience Act).
Regulation (EU) 2024/1772 (Incident Reporting Delegated Regulation).
Regulation (EU) 2024/1774 (Third‑Party Oversight Delegated Regulation).
EIOPA Regulatory Technical Standards on ICT Third‑Party Policy.
ECB TIBER‑EU Framework Guidance.
Commission Delegated Acts C(2024)896 & C(2024)902.
Reduce your
compliance risks

